 Exploit kits
Exploit kits
Exploit kit: A sophisticated attack usually embedded on a website or email. An exploit kit throws a series of specially crafted files, such as a flash movie, PDF document, Java applet, etc at your Internet browser to exploit outdated or non-patched applications that are vulnerable. Once a vulnerable program is found and exploited, the exploit kit executes its payload, usually a virus, to infect the user’s computer.
If you read my previous blog, we bought a custom virus. Now we need to put it on our victims computers. We can hire a hacker to do the work for us. If you also read the “A short history of the Internet” you learned that between 2000 – 2008 we saw the greatest development of the Internet. From static information pages to a dynamic and interactive pages. So what makes the Internet dynamic and Interactive? It’s all the technology we use, Browsers like Internet Explorer, Firefox, Chrome, Safari, etc. and Plugins like java, Adobe’s flash and PDF reader, Apple’s Quicktime, etc. The problem with this fast paced development is that corners are cut and security audit is bypassed to get a new version to the market place. All the programs mentioned above have vulnerabilities.
How viruses are deployed using exploit kits
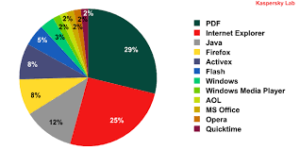
It’s those vulnerabilities that allow a hacker to deploy our virus. Hackers use exploit kits that exploits this vulnerabilities and executes our virus. A hacker will find some vulnerable websites, and inject his exploit kit into them. Then anyone who visits the website will be attacked by the exploit kit silently and if you have any browser or plugins that are out of date the exploit kit executes the payload (our virus).
The hacker will also provide us with the Command & Control console. Usually a hacked website that he has installed the C&C on and give us a login so we can see all the computers infected with our virus. It also keep a count of how many computers were exploited with his exploit kits.